The first step when setting up OpenVPN is to create a Public Key Infrastructure (PKI). In summary, this consists of:
I'd like to generate RSA 1024 key pairs. What I got from google is openssl genrsa -out privatekey.txt 1024 openssl rsa -in privatekey.txt -pubout -out publickey.txtbut why these two files are. Openssl req -nodes -new -x509 -keyout server.key -out server.cert. Here is how it works. Omitting -des3 as in the answer by @MadHatter is not enough in this case to create a private key without passphrase. It is enough for this purpose in the openssl rsa ('convert a private key') command referred to by @MadHatter and the openssl genrsa ('create.
- A public master Certificate Authority (CA) certificate and a private key.
- A separate public certificate and private key pair for each server.
- A separate public certificate and private key pair for each client.
One can think of the key-based authentication in terms similar to that of how SSH keys work with the added layer of a signing authority (the CA). OpenVPN relies on a bidirectional authentication strategy, so the client must authenticate the server's certificate and in parallel, the server must authenticate the client's certificate. This is accomplished by the 3rd party's signature (the CA) on both the client and server certificates. Once this is established, further checks are performed before the authentication is complete. For more details, see secure-computing's guide.
Note:- The process outlined below requires users to securely transfer private key files to/from machines. For the purposes of this guide, using scp is shown, but readers may employ alternative methods as well. Since the Arch default is to deny the root user over ssh, using scp requires transferring ownership of the files to be exported to a non-root user called foo throughout the guide.
- Avoid generating keys on devices without a good entropy source. See [1]. Sometimes, cryptographically secure pseudorandom number generators can be used.
Certificate Authority (CA)
For security purposes, it is recommended that the CA machine be separate from the machine running OpenVPN.
On the CA machine, install easy-rsa, initialize a new PKI and generate a CA keypair that will be used to sign certificates:
Starting from OpenVPN 2.4, one can also use elliptic curves for TLS connections (e.g. tls-cipher TLS-ECDHE-ECDSA-WITH-AES-256-GCM-SHA384). Elliptic curve cryptography provides more security and eliminates the need for a Diffie-Hellman parameters file. See [2] and [3].
Append the following lines to /etc/easy-rsa/vars to make Easy-RSA use elliptic curves:
Now set up PKI and generate a CA certificate:
OpenVPN server files
A functional OpenVPN server requires the following:
- The CA's public certificate
- The Diffie-Hellman (DH) parameters file (required by TLS mode when not using TLS with elliptic curves).
- The server key pair (a public certificate and a private key).
- The Hash-based Message Authentication Code (HMAC) key.
Upon completing the steps outlined in this article, users will have generated the following files on the server:
/etc/openvpn/server/ca.crt/etc/openvpn/server/dh.pem(not when using TLS with elliptic curves)/etc/openvpn/server/servername.crtand/etc/openvpn/server/servername.key/etc/openvpn/server/ta.key
CA public certificate
The CA public certificate /etc/easy-rsa/pki/ca.crt generated in the previous step needs to be copied over to the machine that will be running OpenVPN.
On the CA machine:
On the OpenVPN server machine:
Server certificate and private key
On the OpenVPN server machine, install easy-rsa and generate a key pair for the server:
This will create two files:
/etc/easy-rsa/pki/reqs/servername.req/etc/easy-rsa/pki/private/servername.key
Diffie-Hellman (DH) parameters file
On the OpenVPN server machine, create the initial dh.pem file:
Hash-based Message Authentication Code (HMAC) key
On the OpenVPN server machine, create the HMAC key:
This will be used to add an additional HMAC signature to all SSL/TLS handshake packets. In addition any UDP packet not having the correct HMAC signature will be immediately dropped, protecting against:
- Portscanning.
- DOS attacks on the OpenVPN UDP port.
- SSL/TLS handshake initiations from unauthorized machines.
- Any eventual buffer overflow vulnerabilities in the SSL/TLS implementation.
OpenVPN client files
Client certificate and private key
Any machine can generate client files provided that easy-rsa is installed.
If the pki is not initialized, do so via:
Note: As seen in Certificate Authority section, it is possible to use Elliptic curve instead of RSA for client certificate too by defining EC configuration in/etc/easy-rsa/vars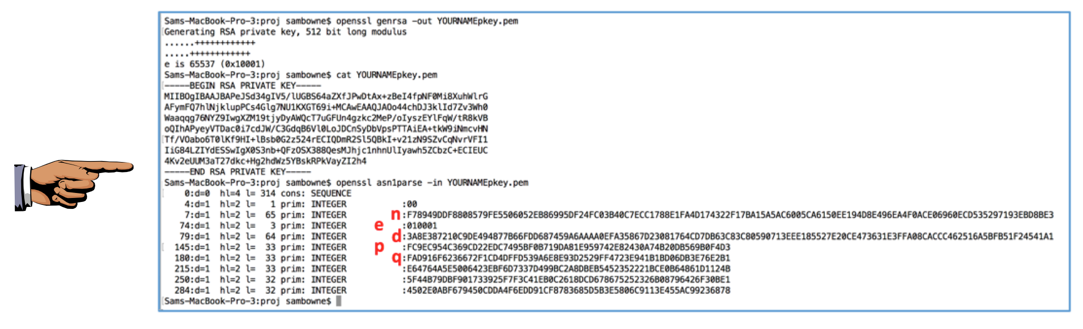 and then exporting it.
and then exporting it.Else it's possible not to use the Environmental Variables and use the corresponding options instead, eg.
Generate the client key and certificate:
This will create two files:
/etc/easy-rsa/pki/reqs/client1.req/etc/easy-rsa/pki/private/client1.key
The gen-req set can be repeated as many times as needed for additional clients.
Sign the certificates and pass them back to the server and clients
Obtain and sign the certificates on the CA
The server and client(s) certificates need to be signed by the CA then transferred back to the OpenVPN server/client(s).
On the OpenVPN server (or the box used to generate the certificate/key pairs):
Securely transfer the files to the CA machine for signing:

On the CA machine, import and sign the certificate requests:
This will create the following signed certificates which can be transferred back to their respective machines:
/etc/easy-rsa/pki/issued/servername.crt/etc/easy-rsa/pki/issued/client1.crt
The leftover .req files can be safely deleted:
Pass the signed certificates back to the server and client(s)
On the CA machine, copy the signed certificates and transfer them to the server/client(s):
On the OpenVPN server, move the certificates in place and reassign ownership.For the server:
For the client:
That is it. To generate the client profile. See: OpenVPN#ovpngen.
Revoking certificates and alerting the OpenVPN server
Revoke a certificate
Over time, it may become necessary to revoke a certificate thus denying access to the affected user(s). This example revokes the 'client1' certificate.
On the CA machine:
This will produce the CRL file /etc/easy-rsa/pki/crl.pem that needs to be transferred to the OpenVPN server and made active there.
Alert the OpenVPN server
On the CA machine:
On the OpenVPN machine, copy crl.pem and inform the server to read it:
Edit /etc/openvpn/server/server.conf uncommenting the crl-verify directive, then restart openvpn-server@server.service to re-read it:
Abbreviated example specifically for containerized Openvpn
This section is specifically for users wanting to run Openvpn in a Linux container (LXC). The code below is designed to be pasted into a root shell; the standard hash has been omitted to allow for easy copy/paste operations. It is recommended to have two different shell windows open, one for the host and one for the container.
Note:- It is assumed that the CA machine is the host and the server machine is the container.
- Both the host and container need to have both openvpn and easy-rsa installed.
- The container needs to be running.
- Define the name of the container in the CONTAINERNAME variable below.
On the host:
In the container:
Back on the host:
That will provide the needed files to make an OpenVPN compatible tunnel profile for the client, and the needed server key files for the server. To generate a client profile, refer to OpenVPN#ovpngen.
See also
- README.quickstart.
- EASYRSA-Advanced.